Cloud computing has made deploying infrastructure faster and more scalable than ever. However, with this flexibility comes a shared responsibility model while the cloud provider secures the underlying infrastructure, you are responsible for securing what runs on it. This is especially true for EC2 instances, which are essentially virtual servers exposed to the internet.
Misconfigurations, outdated software, and weak access controls are some of the most common causes of security incidents in cloud environments. The good news is that most of these vulnerabilities are preventable with the right practices and tools.
In this guide, we’ll walk through the top 10 vulnerabilities commonly found in EC2 instances and provide clear, actionable steps to fix them.
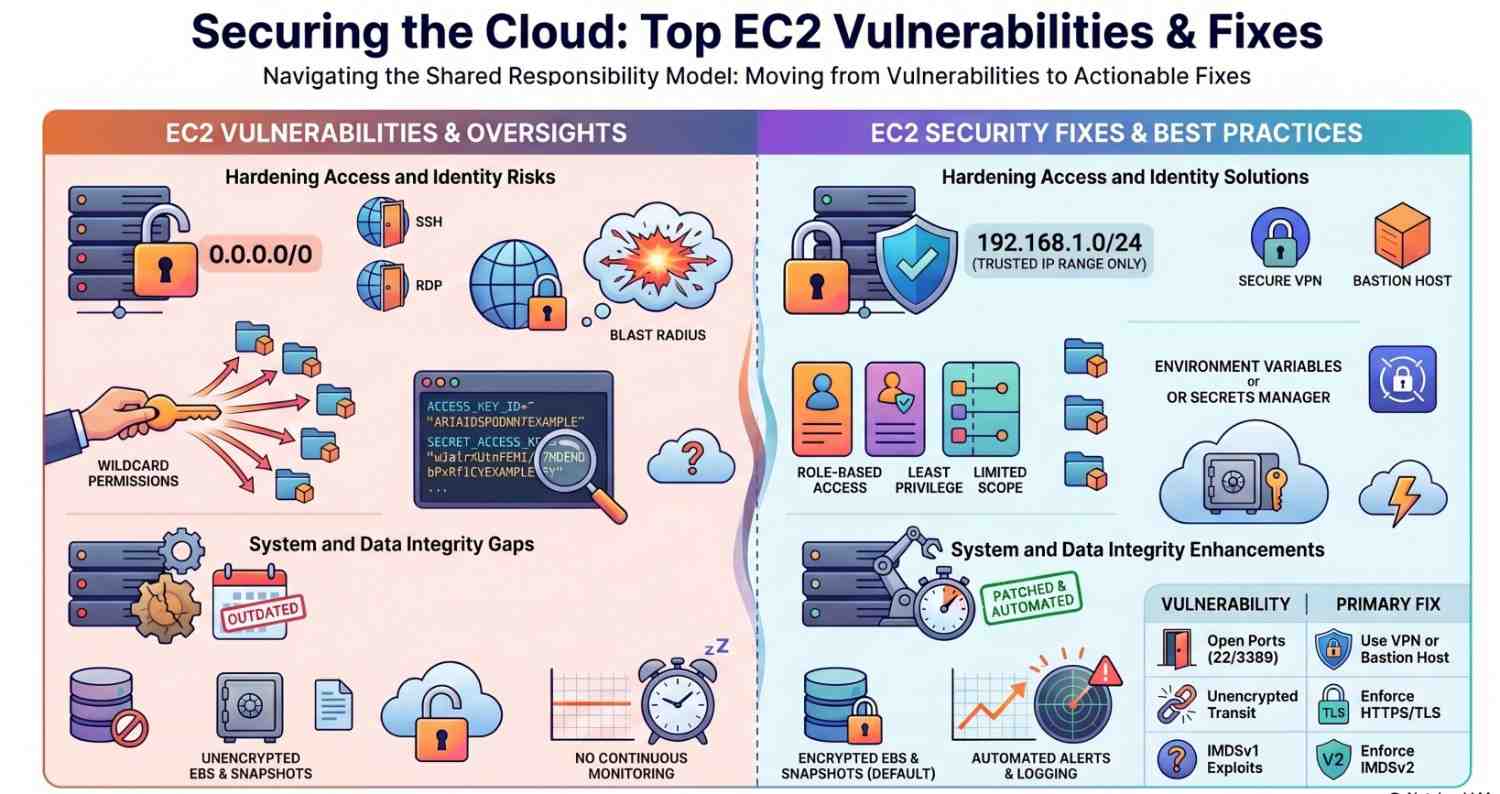
Table of Contents
Toggle1. Unpatched Operating Systems and Software
The Problem
Running outdated OS packages or applications leaves your instance exposed to known vulnerabilities. Attackers often scan for systems with missing security patches.
How to Fix
- Regularly update your system:
sudo apt update && sudo apt upgrade -yorsudo yum update -y - Enable automatic security updates where possible
- Use patch management tools or automation scripts
- Schedule maintenance windows for updates
2. Open Security Groups (Overly Permissive Rules)
The Problem
Security groups acting as virtual firewalls sometimes allow unrestricted access (e.g., 0.0.0.0/0) on sensitive ports like SSH (22) or RDP (3389).
How to Fix
- Restrict access to specific IP ranges
- Avoid exposing SSH/RDP to the public internet
- Use a bastion host or VPN for administrative access
- Regularly audit security group rules
3. Weak or Misconfigured IAM Roles
The Problem
Overly permissive IAM roles attached to EC2 instances can allow unintended access to other AWS services, increasing the blast radius of a compromise.
How to Fix
- Follow the principle of least privilege
- Avoid using wildcard (
*) permissions - Use role-based access instead of hardcoding credentials
- Regularly review and rotate permissions
4. Hardcoded Credentials in Code
The Problem
Storing access keys or secrets directly in application code or configuration files is a major security risk.
How to Fix
- Use environment variables instead of hardcoding secrets
- Store sensitive data in a secrets manager
- Rotate credentials regularly
- Scan repositories for exposed keys
5. Unencrypted Data at Rest
The Problem
If EBS volumes or snapshots are not encrypted, sensitive data can be exposed if accessed improperly.
How to Fix
- Enable encryption for all EBS volumes
- Use default encryption settings for new volumes
- Encrypt snapshots and backups
- Use key management services for better control
6. Unencrypted Data in Transit
The Problem
Data transmitted without encryption (HTTP instead of HTTPS) can be intercepted by attackers.
How to Fix
- Enforce HTTPS using SSL/TLS certificates
- Redirect all HTTP traffic to HTTPS
- Use secure communication protocols (e.g., SFTP instead of FTP)
- Regularly renew certificates
7. Missing or Misconfigured Monitoring
The Problem
Without proper logging and monitoring, detecting suspicious activity becomes difficult.
How to Fix
- Enable logging for system and application activity
- Monitor login attempts and unusual behavior
- Set up alerts for anomalies
- Regularly review logs for suspicious patterns
8. Unused Open Ports and Services
The Problem
Running unnecessary services increases the attack surface. Each open port is a potential entry point.
How to Fix
- Identify running services:
netstat -tulnp - Disable unused services
- Close unnecessary ports in security groups
- Use host-based firewalls for additional control
9. Lack of Endpoint Protection
The Problem
EC2 instances without antivirus or endpoint detection tools are more vulnerable to malware and exploitation.
How to Fix
- Install endpoint protection solutions
- Use intrusion detection systems (IDS)
- Regularly scan instances for malware
- Keep security tools updated
10. Improper Backup and Recovery Configuration
The Problem
Without proper backups, recovering from an attack (like ransomware) becomes extremely difficult.
How to Fix
- Automate backups of EBS volumes
- Store backups securely and separately
- Test restoration procedures regularly
- Implement versioning and retention policies
Bonus: Misconfigured Metadata Service (IMDS)
The Problem
Older configurations of instance metadata service (IMDSv1) can be exploited through SSRF attacks to retrieve credentials.
How to Fix
- Enforce IMDSv2
- Disable IMDS if not required
- Restrict access to metadata endpoints
Best Practices to Stay Secure
Securing EC2 instances is not a one-time task it requires continuous monitoring and improvement. Here are some overarching best practices:
- Implement a defense-in-depth strategy
- Automate security checks wherever possible
- Conduct regular vulnerability scans
- Use infrastructure as code to enforce consistent configurations
- Educate teams about secure coding and deployment practices
Conclusion
Most EC2 vulnerabilities stem from simple oversights open ports, outdated software, or excessive permissions. While these issues are common, they are also highly preventable.
By proactively identifying and fixing these vulnerabilities, you significantly reduce your attack surface and strengthen your cloud security posture. Start with the basics: patch your systems, restrict access, encrypt your data, and monitor everything.
Security in the cloud isn’t just about tools it’s about discipline, consistency, and awareness.
Final Thoughts
If you’re serious about securing your EC2 environment, make vulnerability scanning a regular part of your workflow. Combine automated tools with manual reviews to catch issues early and respond quickly.
A secure cloud environment doesn’t happen by accident it’s built through intentional and continuous effort.
- Want to explore AWS? Click here to get started.





